Apply to IT/OT solution
Reduce Cyber Exposure and the rapid integration of IT/OT the world to ensure the safety of operation
Operating technology (OT) and IT systems integration and the rapid adoption of iot technology to optimize production, promote innovation and improve efficiency.But fusion may expand the attack surface, and introduce more attack vector.
Apply for demo
For industrial operation and important infrastructure industrial safety
Detection of complex and the continuous development of network threats requires advanced tools, knowledge and training.For example, OT environment contains far beyond the OT.Up to half OT environment may also contain equipment based on IT.To prevent attacks and prevent damage need to be able to cope with these two areas at the same time professional ability and the comprehensive safety measures.
For more information on passive fusion, please read thisIT/OT the safety operation guide.
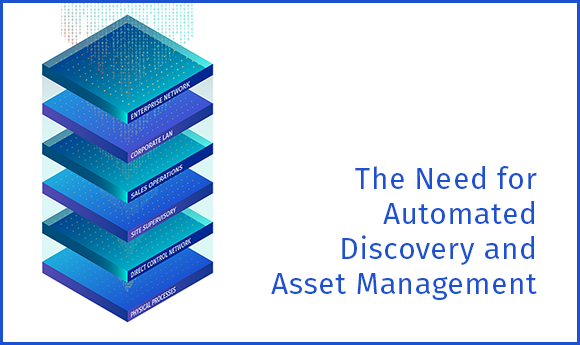
The visibility of whole enterprise
Whether your business is small single site or across complex, distributed environments in hundreds of sites, prevent the attack need to have the ability to see the attack.In the past, isolated IT and OT security practices produced serious blind spots, limiting the detecting vulnerability and the ability to prevent attacks.Tenable OT Security(formerly known as Tenable. Ot) joint Tenable Nessus can eliminate blind spots, and use IT and ot two areas of expertise in the same solution to provide comprehensive network risk exposure of the view.Through the Tenable OT the Security, the enterprise can fully identify potential risks, and faster to solve Security threats.
Tenable OT Security support more than 90% of the PLC products on the market at present, and can be fully integrated with Tenable product combination.In order to make full use of existing IT Security investment, Tenable OT Security can also integrate IT Security products with industry leading enterprises.To this end, we created a set of comprehensive security solution that can take advantage of all security products, and provide unprecedented IT and OT visibility, help enterprises to understand and defend the attack surface.
downloadOT industrial network security environmentSolution outline.
Threat detection and mitigation
useAttack vectorRecognition may attack or by using the field, to take the initiative to find weaknesses in OT environment.By putting a strong network and threat detection engine based on equipment used in combination can be found more threats, these engines from IT or OT, external and internal sources (based on human, extortion software or malware) potential events sounded the alarm.
Tenable OT Security can identify abnormal network behavior and implement network Security strategy and signature and tracking devices change in the local, so that enterprises to detect and preventIndustrial control system (ICS)The risk in the environmental activities.
Custom by fine adjustment strategy, exceptions, and features, the most suitable for the operation of the enterprise security and alarm.Alarm through context awareness and provide the necessary information, details a comprehensive and detailed understanding of the events, and on the basis of making a meaningful response to threats.
downloadForecast OT attackThe white paper.

Asset tracking
Tenable OT Security automation assets find all assets and visual ability provides the most comprehensive, most real-time stock list, including workstations, servers, human-machine interface (HMI), historical records, programmable logic controller (PLC), remote terminal unit (RTU), intelligent electronic devices (ieds) and network equipment.
Tenable patented active query capabilities can be found through network communication dormant equipment.Stock listing to have unparalleled depth of information assets, including tracking firmware and OS version, internal configuration, patch level and users, and IT and the serial number of the OT assets and the bottom configuration.

Accurate find loopholes
Take the initiative to identify and repair loophole, from attacker to use.Using the asset tracking ability, comprehensive and detailed Tenable OT Security passBug priority rating (VPR)Generate related threat rating and classification list.The ratings of a particular device based on the environment, as well as the firmware version, related CVE, Tenable proprietary research, the default password, open ports, installed patches, and other parameters.The report contains a detailed insight and alleviate advice.
Insight into thePredict priority analysis.
Configuration control
Tenable OT Security malicious software and the user can be traced through the network or changes to the equipment to perform directly.Tenable OT Security提供了设备配置随时间变化的完整历史记录,包括特定梯形逻辑段、诊断缓冲区、标签表等细分记录。 这使得管理员能够建立带有“上一个经过确认的良好状态”的备份快照,从而加快恢复并遵守业内法规。

Make full use of Tenable ecosystem "trust"
Give full play to the existing security investment.TenableOT Security 与Tenable Security CenterandTenable Vulnerability Management,Fully integrated, can provide the whole fusion operations on complete visibility, security and control function.Tenable OT Security and Tenable Identity Exposure can identify the hand in hand may lead to OT in the environment blackmail error Active Directory configuration software attacks and threats.Tenable OT Security also can be used with the IT service management, a new generation of firewall (NGFW) and Security information and event management (SIEM) suppliers and other IT Security technology to conduct a comprehensive integration.
Using the Tenable product line integration and cooperation, and the industry's leading IT and OT safety systems, you will get security operations against IT and OT threat today the full situational awareness.
readingTenable power solutions in OT in the environmentThe white paper for more information.

Information graph
OT and ICS security environment of the network threat situation
The top three industries OT attack
View information figureRelated products
Check the Tenable OT the Security
The practical application of
"We further study of the various solutions.Of course is Tenable."Matt Ramberg Sanmina, vice President of information security department


